According to Kaspersky Labs, almost all of the computers infected with WannaCry (WCry, WannaCrypt) were running Windows 7. A small percentage (less than 1%) were running Windows XP.
Microsoft released updates in March 2017 which — if installed — protect Windows 7 computers from WannaCry infections. So all those Windows 7 WannaCry infections were only possible because users failed to install updates. This is a good argument for either enabling automatic updates, or being extremely diligent about installing updates as soon as they become available.
A researcher at Quarkslab discovered a method for decrypting files encrypted with WannaCry, although it only works on Windows XP, and only if the computer has not been restarted since the files were encrypted.
Building on the discoveries of Quarkslab, researchers at Comae Technologies and elsewhere developed a tool that can decrypt files encrypted by WannaCry on Windows 7 as well as XP. The new tool — dubbed wanakiwi by its developers — uses the same technique as its predecessor and has the same limitation: it doesn’t work if the infected computer has been restarted since encryption occurred.
The Register points out that while the NSA was hoarding exploits, Microsoft was doing something similar with patches. Microsoft is in fact still creating security updates for Windows XP and other ‘unsupported’ software; they just don’t normally make those updates available to the general public. Instead, they are only provided to enterprise customers, which pay substantial fees for the privilege. When Microsoft released the Windows XP patch in response to the WannaCry threat, the patch was already developed; all Microsoft had to do was make it available to the general public. Sure, developing updates costs money, and Microsoft wants to recover those costs somehow, but it seems clear that we would all be better off if they made all updates available to everyone.
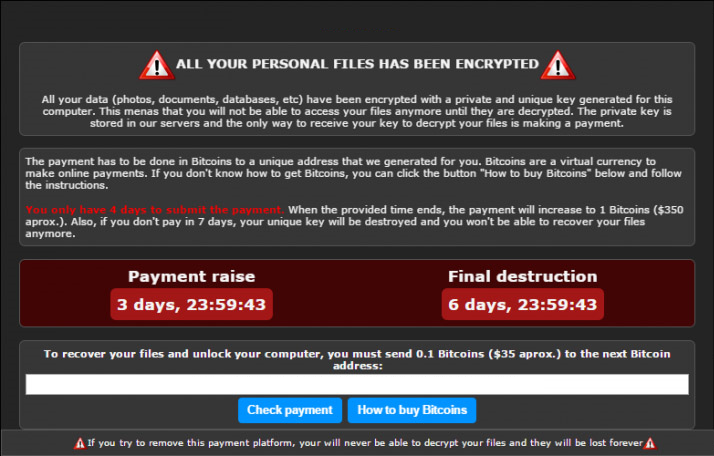
Bruce Schneier provides a useful overview of WannaCry, and how best to protect yourself. From the article: “Criminals go where the money is, and cybercriminals are no exception. And right now, the money is in ransomware.”
Update 2017May21: Analysts have confirmed that WannaCry’s initial infections were accomplished by scanning the Internet for computers with open Server Message Block ports, then using the EternalBlue SMB exploit to install the ransomware. Once installed on any computer, WannaCry spread to other vulnerable computers on the same local network (LAN). Earlier assumptions about WannaCry using spam and phishing emails to spread were not accurate.
 boot13
boot13