 Yesterday I fired up my media PC, booting to Windows 10, to watch some episodic visual media (you know, TV shows) that we refer to as ‘comfort food’ around here.
Yesterday I fired up my media PC, booting to Windows 10, to watch some episodic visual media (you know, TV shows) that we refer to as ‘comfort food’ around here.
Imagine my surprise when instead I saw a series of weird dialog boxes pop up on the screen, many of which were blank. Was it some kind of malware? Nope, it was Microsoft Copilot, trying to install itself and going berserk.
I tried following the prompts I was able to see, but those just led to more dialogs, including prompts for a PIN code that I don’t normally use when logging in. On that computer, I had previously given in to Microsoft’s increasingly strident demands that I use a Microsoft account to log in. So the PIN prompt was confusing.
I wish I had taken video of the whole thing. It was both comical and horrifying. My roommate looked on while I tried in vain to close blank dialogs that kept recreating themselves.
Eventually I recognized the Copilot logo on the taskbar for some of these dialogs, and caught enough of one briefly-flashed message to realize that this was Copilot, apparently attempting to install itself.
Windows 10 marked a major change in the way Microsoft updates the operating system: basically, updates are pushed to your computer whether you want them or not. You can delay them, sort of, but you can never stop them completely.
I have serious misgivings about that, but also about Microsoft’s decision to push Copilot to PCs running a version of Windows that won’t even be supported in a few months. Windows 10 support will end in October of 2025.
Anyway, once I realized that the barf being spewed in my face by Microsoft was related to Copilot, something in which I have zero interest, I started killing tasks. The ensuing game of whac-a-mole went on for a few minutes before I finally won, and the insane dialogs stopped appearing.
I then proceeded to remove Copilot-related garbage from the Startups list, which I later confirmed did in fact stop this mess from occurring again at the next startup.
That was half an hour of my life that I will never get back. Thanks, Microsoft!
Luckily, I was only booting to Windows on my media PC temporarily, while working on a minor problem with Linux Mint on the same PC. I’ve now gone back to using Linux Mint, and I really hope I never have to boot to Windows 10 again.
Ever since Microsoft throttled back their own update testing, instead relying on problem reports from canaries (literally how Microsoft refers to people who opt in to receive Windows updates early), the number of problems resulting from updates has increased sharply (full disclosure: I only have anecdotal evidence of this).
Here’s another example of Microsoft update fun: a couple of weeks ago, Outlook stopped working on all PCs at a client’s location. After a lot of troubleshooting, it eventually became clear that a recent Microsoft update had hosed Office. The Office ‘repair’ function fixed most of the PCs, but on one, Office had to be reinstalled completely. Frustrating, annoying, and totally unnecessary.
Come on, Microsoft. You used to be just kind of shitty. Now it seems like you actively hate your users.
 boot13
boot13 The folks at Microsoft are once again demonstrating their creativity in thinking up ways to trick people into using its web search service, Bing.
The folks at Microsoft are once again demonstrating their creativity in thinking up ways to trick people into using its web search service, Bing.
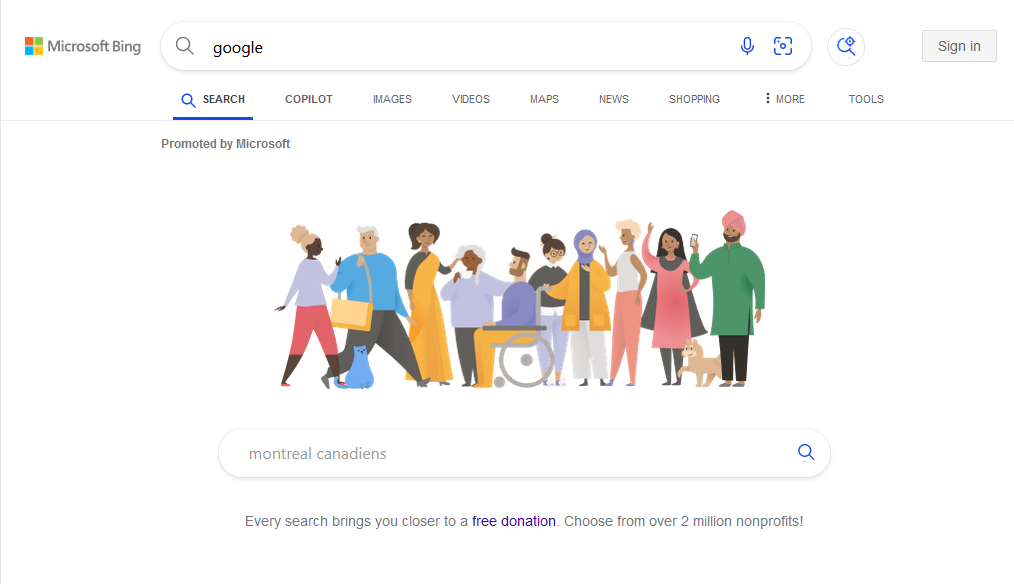
 There’s apparently a team of people at Microsoft who spend all their time trying to come up with sneaky ways to get Windows users to switch to Edge as their default web browser. To be clear, I have no direct evidence that such a team exists, but it seems likely.
There’s apparently a team of people at Microsoft who spend all their time trying to come up with sneaky ways to get Windows users to switch to Edge as their default web browser. To be clear, I have no direct evidence that such a team exists, but it seems likely. I was just
I was just  Here are the first two paragraphs of a
Here are the first two paragraphs of a  Some technologies seem always to be just around the corner. Every few years, people get excited all over again, about 3D media, virtual reality, voice assistants, hoverboards, self-driving cars, flying cars, artificial intelligence, and other things that always turn out to be more hype than anything else.
Some technologies seem always to be just around the corner. Every few years, people get excited all over again, about 3D media, virtual reality, voice assistants, hoverboards, self-driving cars, flying cars, artificial intelligence, and other things that always turn out to be more hype than anything else. Until June 30, Microsoft had planned to disable Visual Basic for Applications (VBA) scripts in Office applications. VBA is the programming language built into all Office applications.
Until June 30, Microsoft had planned to disable Visual Basic for Applications (VBA) scripts in Office applications. VBA is the programming language built into all Office applications.