 A recently-discovered bug in newer versions of Windows is causing bizarre local time shifts.
A recently-discovered bug in newer versions of Windows is causing bizarre local time shifts.
Keeping accurate time on computers is important for a lot of reasons, many of which are not obvious to non-technical users. Update schedules, scheduled background tasks, synchronization with server and cloud resources, and many other time-sensitive processes depend on your PC maintaining accurate time.
Because it’s so important, and because various factors can sometimes cause a PC’s clock to drift, operating systems use a variety of methods to check and adjust it. The most obvious of these in Windows can be seen in Windows 10 and 11 in Settings > Time & Language. Windows regularly compares the PC’s clock with an Internet-based clock, such as time.windows.com. When a discrepancy is observed, the PC’s clock is updated.
Between a PC’s internal clock and Windows’ time synchronization, most Windows-based computers are able to maintain accurate time.
But at some point, someone at Microsoft decided that Windows needed additional time checks. So they created something called Secure Time Seeding. This function regularly analyzes secure network traffic from a ‘known good’ host computer, and calculates the current time based on what it sees.
Sounds good, right? Anything that makes the clock more accurate is good, right? Well, no. There’s at least one major problem with Secure Time Seeding, which causes it to get confused about the date and time, and can set your computer’s time based on random values. This has been observed to incorrectly change the Windows clock by minutes, hours, days, or more. As you can imagine, this causes all manner of strange problems.
Microsoft’s response to the report of this bug has been disappointing: they are downplaying its scope and effects. And while it’s true that there are very few reports of this happening, the problems it can cause are bad enough that anyone running Windows 10 and up or Windows Server 2016 and up should disable Secure Time Seeding.
To disable Secure Time Seeding on a Windows 10 or 11 PC, follow the instructions provided by Microsoft.
Trying to make sense of the actions and statements of a corporate behemoth like Microsoft is an exercise in futility. It’s possible that they will realize that this bug is actually very bad, and fix it, or they may find a way to limit its effects, or they may change the feature so that it’s disabled by default. But in the meantime, there are potentially millions of computers out there that might start exhibiting strange clock problems for the forseeable future.
 boot13
boot13 I was just
I was just  Here are the first two paragraphs of a
Here are the first two paragraphs of a  As I’m sure you’ve noticed by now, I’m using
As I’m sure you’ve noticed by now, I’m using 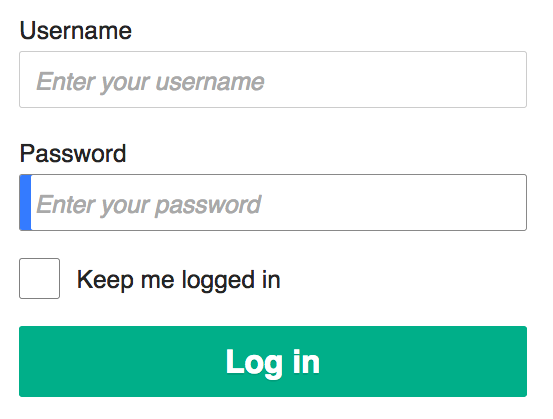 Using a password manager is still the best way to securely record all your passwords. This assumes that you are in fact using different passwords for every web site and service that require one. If you’re using the same password for everything, you are risking your privacy, financial security, and sanity.
Using a password manager is still the best way to securely record all your passwords. This assumes that you are in fact using different passwords for every web site and service that require one. If you’re using the same password for everything, you are risking your privacy, financial security, and sanity. Some technologies seem always to be just around the corner. Every few years, people get excited all over again, about 3D media, virtual reality, voice assistants, hoverboards, self-driving cars, flying cars, artificial intelligence, and other things that always turn out to be more hype than anything else.
Some technologies seem always to be just around the corner. Every few years, people get excited all over again, about 3D media, virtual reality, voice assistants, hoverboards, self-driving cars, flying cars, artificial intelligence, and other things that always turn out to be more hype than anything else.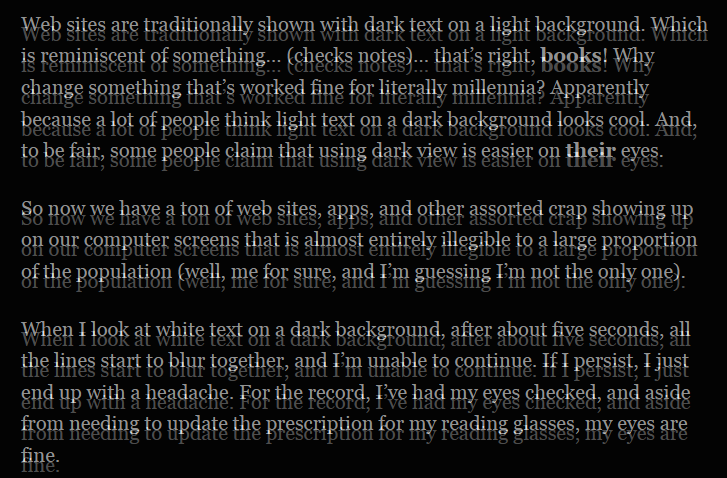
 Until June 30, Microsoft had planned to disable Visual Basic for Applications (VBA) scripts in Office applications. VBA is the programming language built into all Office applications.
Until June 30, Microsoft had planned to disable Visual Basic for Applications (VBA) scripts in Office applications. VBA is the programming language built into all Office applications.