 Using a password manager is still the best way to securely record all your passwords. This assumes that you are in fact using different passwords for every web site and service that require one. If you’re using the same password for everything, you are risking your privacy, financial security, and sanity.
Using a password manager is still the best way to securely record all your passwords. This assumes that you are in fact using different passwords for every web site and service that require one. If you’re using the same password for everything, you are risking your privacy, financial security, and sanity.
So… which password manager should you use? Most of the major password management services (1Password, LastPass, etc.) store your passwords on their own servers, and there’s no question that this provides some benefits in terms of convenience, with the main one being that you can access your passwords from anywhere. You don’t have to back up your password data or copy it between devices; it’s maintained by the service provider and easily accessible via their web site.
But this convenience comes at a huge cost: the risk that your passwords will be compromised when the service provider experiences a security breach.
A recent breach at LastPass is, sadly, only the most recent example. In this case, the LastPass servers were compromised and attackers gained access to user data. The company first reported the breach in August 2022, but downplayed the impact on users. Their latest announcement finally provides the full story, and acknowledges that the attackers gained full access to user data, including encrypted passwords.
More about the breach from Bruce Schneier.
Although LastPass is to blame for the breach and compromised user data, passwords in the user data obtained by the attackers are all encrypted, and there’s no way to magically decrypt them without knowing the master passwords of individual users. However, that just means that the people who have the data will be using brute-force techniques to crack those passwords. For users whose master password is long and complex, it would take years–if not centuries–to crack, but if your master password is simple or commonly-used, all of your passwords are now known by these attackers.
Something for your to-do list: if you use LastPass, and your master password is easy to crack (check it here), you should immediately change ALL of your passwords.
In my opinion, you’re much better off using password management software that stores its data locally, on your own computer. Then you only need to worry about someone getting access to your computer, which you can actually control.
I’ve long recommended Password Corral for Windows users. It’s simple, secure, and free, and it stores its data locally only.
Other password managers that use only local storage include PasswordSafe, KeePassXC, and KeeWeb. Password managers that can be used with local storage include Roboform, and Sticky Password.
And remember that when you use a ‘cloud’ service, you’re just storing your data on a total stranger’s computer, which may or may not be managed and secured competently, and which you have basically no control over. Cloud stuff is convenient, but the risks of using it indiscriminantly are enormous.
Update 2023Sep11: Brian Krebs reports that password information obtained during this breach is being actively used by criminals to gain unauthorized access to various systems and services.
 boot13
boot13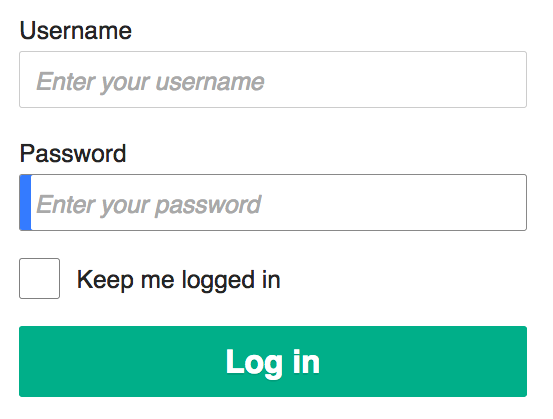 Using a password manager is still the best way to securely record all your passwords. This assumes that you are in fact using different passwords for every web site and service that require one. If you’re using the same password for everything, you are risking your privacy, financial security, and sanity.
Using a password manager is still the best way to securely record all your passwords. This assumes that you are in fact using different passwords for every web site and service that require one. If you’re using the same password for everything, you are risking your privacy, financial security, and sanity. People use VPNs (Virtual Private Networks) for lots of reasons, both legitimate and… less so. They are commonly required for remote access to workplace computers by employees. They are used by people who do their banking from public WiFi networks. They are used by people who can’t afford to pay for dozens of streaming and cable services and instead rely on still-considered-illegal downloads of copyrighted media. And some people use VPNs to get around ridiculous regional limitations on access to streaming media.
People use VPNs (Virtual Private Networks) for lots of reasons, both legitimate and… less so. They are commonly required for remote access to workplace computers by employees. They are used by people who do their banking from public WiFi networks. They are used by people who can’t afford to pay for dozens of streaming and cable services and instead rely on still-considered-illegal downloads of copyrighted media. And some people use VPNs to get around ridiculous regional limitations on access to streaming media. Pegasus is spyware that can be installed on Apple and Android mobile systems. It’s difficult to detect, and difficult to remove. Pegasus is developed by NSO Group, who deny that the software is being used for anything nefarious, or that if it is, that use has nothing to do with NSO Group.
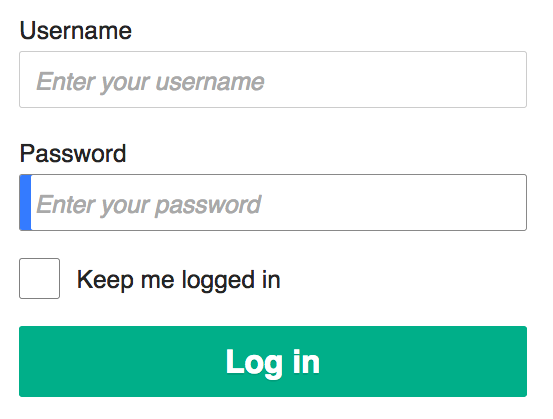
Pegasus is spyware that can be installed on Apple and Android mobile systems. It’s difficult to detect, and difficult to remove. Pegasus is developed by NSO Group, who deny that the software is being used for anything nefarious, or that if it is, that use has nothing to do with NSO Group.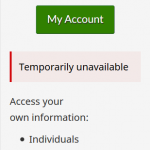 Canadians: if you’ve tried to access your CRA accounts recently, you probably noticed that you can no longer log in. That’s because normal access has been disabled while the CRA works to undo the damage caused by two recent attacks on their services.
Canadians: if you’ve tried to access your CRA accounts recently, you probably noticed that you can no longer log in. That’s because normal access has been disabled while the CRA works to undo the damage caused by two recent attacks on their services. A
A