 I’m sure that Russia is a wonderful place, and I’m sure that the vast majority of people there are lovely, and have no interest in harming anyone.
I’m sure that Russia is a wonderful place, and I’m sure that the vast majority of people there are lovely, and have no interest in harming anyone.
Sadly, from the perspective of a server operator, it sometimes feels that nothing good ever comes from Russia.
Being the diligent server operator that I (hopefully) am, I monitor things pretty closely. That includes network traffic coming from the Internet. Over the years, I’ve noticed that a huge proportion of the probes, DDoS attacks, spam, phishing, and hack attempts against my network come from IP addresses in Russia.
It’s gotten to the point where I am now actively blocking huge swathes of Internet addresses (IPs) that originate in Russia and neighbouring countries like the Ukraine.
Blocking those nasty IPs
I run a Linux web server, as well as several Internet-enabled services, at my home office. All of the communications between my server and the Internet pass through a router, making it the ideal place to block unwanted traffic for my entire network, which includes media computers, development systems, and the Windows computer on which I’m writing this.
I’m using a commercial router, but I’ve replaced the original firmware with Advanced Tomato. Doing this provides many benefits, including making it easier to manage the router’s firewall, IPTABLES. Here’s a typical IPTABLES command to block an IP address from the router’s Linux command line:
iptables -I FORWARD -s 185.219.52.90 -j DROP
The DROP directive tells the router to unceremoniously drop any traffic from the specified IP, without logging this action. Traffic can also be logged when it’s dropped, but excessive logging can cause performance problems and fill up logs with junk, so I just drop this traffic.
I issue commands like the one above at my router’s command line to block the traffic immediately, and then I update the router’s startup firewall script with the same command, so that it persists after the next router restart.
So there’s this one guy
There’s been one particularly persistent attacker in the last year or so. This person wants desperately to gain access to one of my Internet-accessible services, but he’s not particularly intelligent, because he keeps trying the same things over and over, in rapid succession. So much so, that at times the traffic he generates comes within shouting distance of a DDoS attack.
I started paying particular attention to traffic associated with a series of ports that are used by the service, and blocking the IP addresses at the other end of that traffic. Whereupon we embarked upon a long game of whac-a-mole, in which I blocked an IP or IP range, and the attacker moved to another host or VPN provider and resumed his attacks from there. It seems clear that this was all being done by one attacker, based on his quick reactions to my blocking.
This went on for several months, but now he appears to have given up. Or at least he’s moved on to other methods.
In the process of blocking all these IPs and networks, the attacker has also helpfully provided me with a list of VPN providers that should be blocked by, well, everyone. Everyone who doesn’t specifically need to allow them.
IP addresses and ranges I’m blocking
Almost all of these IPs and IP ranges are in Russia and the Ukraine. A few are elsewhere in Asia. Most of the ranges are VPN providers.
103.48.51.116
104.129.18.0/23
104.237.192.0/19
104.237.203.0/24
141.98.10.0/24
173.244.208.60
176.67.85.0/24
185.156.72.0/24
185.156.74.0/24
185.193.88.0/24
185.217.69.157
185.219.52.112
185.219.52.90
185.219.52.91
193.106.191.25
193.106.191.35
193.106.191.41
193.32.164.85
193.93.62.0/24
195.54.160.27
198.8.81.220
216.131.114.0/24
216.131.116.0/23
216.131.68.0/24
216.131.88.0/23
217.138.255.202
31.43.185.29
31.43.185.9
37.120.218.0/24
45.134.26.0/24
45.143.203.121
45.145.64.0/23
45.145.65.11
45.146.164.0/23
45.146.166.0/23
45.155.204.0/24
45.155.205.0/24
45.227.253.0/24
45.9.20.0/24
5.188.206.230
71.19.251.0/24
76.180.16.74
77.243.191.120
77.83.36.0/24
78.128.112.18
82.145.32.0/19
84.17.41.141
84.17.41.151
87.251.75.0/24
89.187.182.87
89.187.183.76
91.191.209.110
92.204.240.75
92.255.85.0/24
94.232.40.0/21
98.175.213.148
Here are a few other ranges I’m blocking for various reasons:
- Hungarian ISP MAGYAR-TELEKOM-MAIN-AS IP range (unceasing garbage):
94.27.128.0/17
- MediaLand BPH IP range (generally just horrible):
45.141.84.0/24
- EE-GIGAHOSTINGSERVICES (constant email relay attempts):
176.111.173.0/24
 boot13
boot13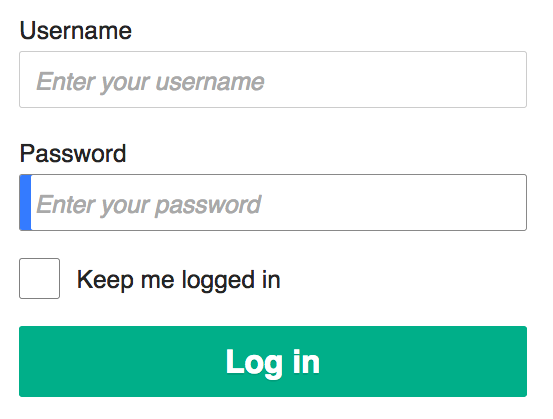 Using a password manager is still the best way to securely record all your passwords. This assumes that you are in fact using different passwords for every web site and service that require one. If you’re using the same password for everything, you are risking your privacy, financial security, and sanity.
Using a password manager is still the best way to securely record all your passwords. This assumes that you are in fact using different passwords for every web site and service that require one. If you’re using the same password for everything, you are risking your privacy, financial security, and sanity. Until June 30, Microsoft had planned to disable Visual Basic for Applications (VBA) scripts in Office applications. VBA is the programming language built into all Office applications.
Until June 30, Microsoft had planned to disable Visual Basic for Applications (VBA) scripts in Office applications. VBA is the programming language built into all Office applications. I’m sure that Russia is a wonderful place, and I’m sure that the vast majority of people there are lovely, and have no interest in harming anyone.
I’m sure that Russia is a wonderful place, and I’m sure that the vast majority of people there are lovely, and have no interest in harming anyone. Time for another thrilling game of I Hope These Critical Security Updates Don’t Break Anything On My Computer with your permanent host, Microsoft.
Time for another thrilling game of I Hope These Critical Security Updates Don’t Break Anything On My Computer with your permanent host, Microsoft. Oracle just released its quarterly
Oracle just released its quarterly