About twenty bug fixes and minor changes made it into the latest version of Chrome, 57.0.2987.110. None of the changes seem to be related to security. The announcement doesn’t mention anything about what changed, but the full change log — refreshingly small this time — lists all the changes in detail.
All posts by jrivett
Vivaldi 1.7.735.48
A minor security issue in its installer prompted the release of Vivaldi 1.7.735.48 yesterday. The browser itself isn’t changed in this release – only its installer – but its version number was bumped up from 1.7.735.46 anyway. If you’re already running Vivaldi 1.7.735.46, there’s no need to update, and the browser won’t bother to update itself.
Patch Tuesday updates from Microsoft and Adobe
It looks like Microsoft fixed the technical issues that led to February’s updates being postponed until March. Today they announced eighteen updates that address security issues in Windows, Internet Explorer, Edge, Office, Silverlight, as well as Windows Server software, including Exchange.
Critical vulnerabilities for which updates were expected in February, including an SMB flaw in Windows (CVE-2017-0016), and two others that were disclosed by Google’s Project Zero that affect the Windows GDI library (CVE-2017-0038), and Internet Explorer and Edge (CVE-2017-0037), finally get fixes today.
A total of one hundred and forty vulnerabilities are addressed by today’s updates from Microsoft. That’s higher than usual, but of course this is two months’ worth of updates.
Adobe’s contribution to the patching fun this month is new versions of Flash and Shockwave. Flash 25.0.0.127 includes fixes for seven vulnerabilities in earlier versions, while Shockwave 12.2.8.198 resolves a single security issue in versions 12.2.7.197 and earlier.
Chrome will update itself with the new version of Flash in the next day or so, but you can usually trigger the update process by navigating to its About page. Flash updates for Internet Explorer and Edge are included in this month’s updates from Microsoft.
If you’re still using a web browser with a Flash plugin, you should make sure it’s up to date as soon as possible.
Update 2017Mar17: Ars Technica points out — quite rightly — that Microsoft still owes us all an explanation for why the February updates were cancelled. My favourite quote from the Ars article: “when marketers drive communications concerning a reported zero-day exploit, customers lose.” I’d argue that when marketing folk are the only ones talking about technical issues of any kind, we should all be very worried.
Why your Wi-Fi sucks
There’s an entertaining and illuminating post over at Ars Technica that gets into the nitty-gritty of exactly why wi-fi connections are so slow and generally… crappy.
I manage wi-fi networks in my own home and for clients. But I barely use them myself, and then only for my mobile devices, and only for basic functions. I’ve long since given up on the idea of using wi-fi for the bulk of my networking needs. All of my personal and professional experience has shown that wi-fi is only useful in terms of convenience.
The Ars Technica writer who penned the post, Jim Salter, apparently feels the same way. But he goes a lot further, with clear explanations for the problems you deal with when using wi-fi. And he has some good advice: don’t use wi-fi unless you have to; the more you use it, the worse it performs.
Chrome 57.0.2987.98
The latest version of Chrome includes fixes for thirty-six security vulnerabilities.
There are numerous other changes in Chrome 57.0.2987.98. Google didn’t see fit to highlight any of them in the release announcement, so you’ll have to read the browser-annihilating change log to see if any of the changes are of interest. I’m not planning to do that myself, as it’s likely to take several hours, and unlikely to be particularly rewarding.
Chrome updates itself on its own mysterious schedule, but you can usually trigger an update by going to its ‘About’ page. Because this version includes security updates, you should try to update Chrome as soon as possible.
Update 2017Mar16: Ars Technica points out that Chrome 57 includes power saving features that should extend battery life for Chrome users on laptops.
They’re here: ads in Windows 10
We called it. Microsoft denied it. Now the reality of advertising in Windows has arrived. We’re not talking about the tiny, easily-ignored ads commonly seen in Skype, either. The ads that just started appearing in Windows 10 are hard to miss, and they’re in Windows Explorer, arguably the core user interface of the system.
Of course Microsoft is calling these ads ‘tips’ and insists that they just provide helpful information to Windows 10 users. Okay, let’s take a look at what users are seeing:
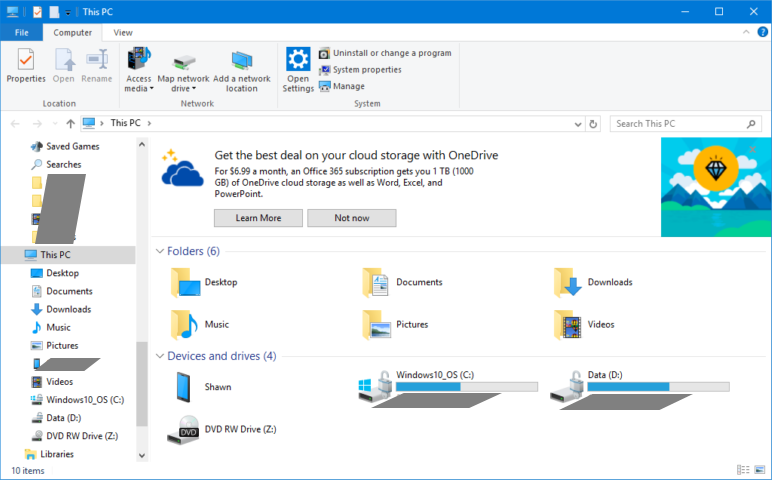
You may disagree, but in my opinion, that’s an ad. It might as well say “Your Advertisement Here” or “Advertise In This Space”. At this stage, I’m sure we’ll only see ads from Microsoft in Explorer, but once the anger subsides, it’s difficult to imagine Microsoft won’t start selling that space – and others like it – to the highest bidder.
That’s right, Windows 10 really is an advertising platform, just as we’ve been saying all along. It explains why Microsoft was so happy to give away the O/S to anyone who upgraded from an earlier version, why they pushed so hard and literally tricked people to upgrade from earlier versions, why they included so much user activity tracking in Windows 10, and why they retrofitted that tracking into earlier versions when people failed to upgrade in sufficient numbers.
Clearly, the underlying reason for Microsoft’s advertising-in-Windows strategy is simply the enormous amount of money being made by Google from advertising.
Linux is looking a lot better now, isn’t it?
Analysis from The Verge and Ars Technica.
Update 2017Mar17: Tom Warren over at The Verge reacts to the new ads in Windows 10. He describes it as an ‘infestation’, and I agree with his assessment.
Firefox 52 – security fixes, WebAssembly support
At this point it seems clear that Mozilla has instructed its content writers to never mention version numbers in Firefox release announcements. The reason remains a mystery. Take yesterday’s announcement, for example. It begins “Today’s release of Firefox” – which makes it sound like Firefox is a new product.
Anyway… the mystery Firefox release yesterday was in fact version 52, which fixes at least twenty-eight security vulnerabilities. The new version also adds support for WebAssembly, which can dramatically improve the performance of web-based applications. Support for those annoying WiFi ‘captive portal’ hotspot login pages is improved in Firefox 52, and there are further improvements to the warnings you’ll see when you’re presented with a login form on an unencrypted connection.
Firefox 52 also removes almost all remaining support for the NPAPI plugin technology, with the lone exception being Flash, which means Silverlight, Java, Acrobat and other plugins that depend on NPAPI will no longer work. Support for the NPAPI version of Flash will apparently be removed in the next major Firefox release.
WordPress 4.7.3 fixes six security issues
If you manage any WordPress web sites, you should make sure that they are now running version 4.7.3. The new version addresses six security vulnerabilities, and includes about forty other minor changes.
Most WordPress sites are configured to install security updates like this automatically, but it’s a good a idea to check.
Microsoft announces amazing new Windows 10 feature
There’s a surprisingly lengthy post on the Windows Experience blog, co-written by two senior Microsoft managers: Michael Fortin (CVP of Windows and Devices Group Core Quality) and John Cable (Director of Program Management, Windows Servicing and Delivery).
Okay, what’s so important that these two folks decided to write about it? Just this: after the upcoming Windows 10 “Creators Update”, Windows 10 will be slightly less likely to do things at inconvenient times.
I don’t know about you, but allowing users to have control over when updates are installed, and when their computer reboots, seems like a pretty basic feature. And in fact that kind of control has existed in Windows for years. Until Windows 10. But instead of fixing the problem and apologizing for it, we get senior Microsoft managers talking about this bug fix as if it was the most amazing new feature ever.
I understand that there are good reasons to force updates and restarts, the main one being that otherwise many people allow their computers to get out of date, and vulnerable. But seriously, wouldn’t it have made more sense for automatic updates and restarts to be the default behaviour, and allow for this behaviour to be overridden, when Windows 10 was released?
The Verge’s take on this. And Ars Technica’s.
Update 2017Mar22: A new ‘tip’ from Microsoft shows Windows 10 users how to change ‘Active Hours’, during which Microsoft hopefully won’t remotely restart their computer. Of course, the maximum duration for active hours is still only twelve hours. On a related note, I was wondering why my Windows 10 test PC always seemed to be logged out lately, and discovered that it’s been trying to install one particular update every night for a couple of weeks. Windows reboots to complete the install, but the installation fails, and the cycle repeats. This is exactly the kind of thing that bothers me about letting Microsoft screw around with my computer without my knowledge.
Opera 43.0.2442.1144
A new version of Opera fixes a few minor bugs, none of which involve security. The full change log for Opera 43.0.2442.1144 has additional details.
 boot13
boot13